by Regents Risk Advisory | Mar 19, 2011 | Fraud & Integrity, Fraud Money Laundering
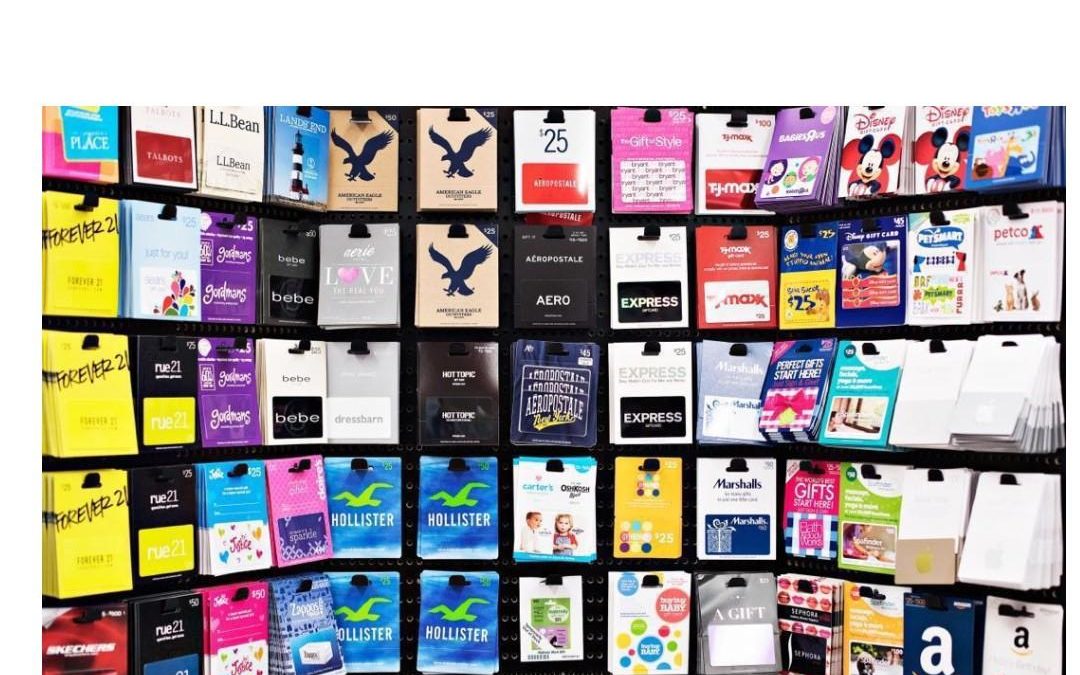
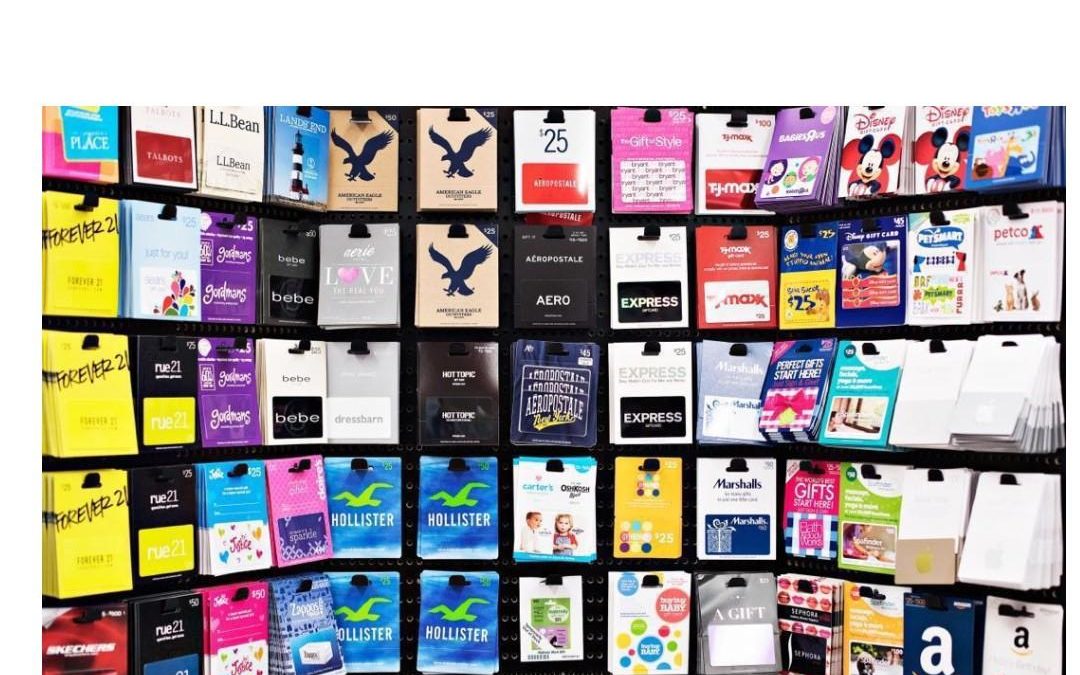
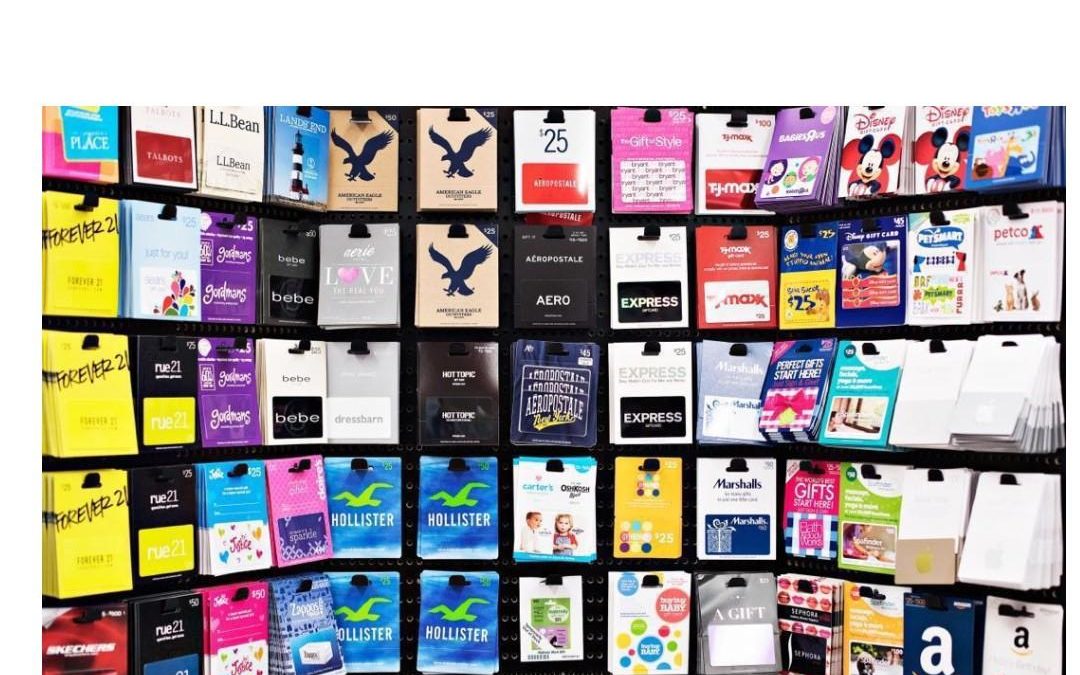
Gift card vouchers can be the perfect solution for a birthday when you’re not sure which present to buy. Simply pay cash at the store or shopping mall and transfer the same value onto the voucher to be used at the designated outlets. Travellers Cheques have been...

by Regents Risk Advisory | Mar 5, 2011 | Cyber-Threat, Data Security, Forensic Data & Cyber Threats
Most people are lazy when it comes to using computers properly. People are even lazier when to comes to selecting a password for accessing their computer or web service. Computer security seems to be a keyboard type too far. The more complex a password is by...